
The ClickFix campaign has rapidly evolved from a relatively noisy, disk-heavy infection chain into a sophisticated, highly obfuscated threat. By leveraging fake CAPTCHA verification pages (like fabricated Cloudflare or Google reCAPTCHA prompts), attackers trick users into copying and pasting malicious PowerShell commands directly into their terminals.
As defenders have caught on to these social engineering tactics, the underlying payloads have undergone a significant evolution to evade detection.
In its earlier iterations, the ClickFix attack chain was relatively straightforward and left a noticeable footprint on the host system.

Stage 1: The victim executes a cleartext PowerShell command (e.g., Invoke-WebRequest).
Stage 2: The command connects to an attacker-controlled server and downloads a secondary batch script (ct.bat) directly to the %TEMP% directory.
Stage 3: This batch script executes, retrieving and launching the final payload—in this case, the DeerStealer InfoStealer, which immediately begins harvesting browser data, crypto wallets, and system information.
Because the payload was dropped to disk and the initial PowerShell commands lacked advanced obfuscation, standard endpoint detection and response (EDR) solutions could flag the anomalous .bat execution from the Temp folder relatively easily.
To bypass these static defenses, the threat actors drastically upgraded their methodology. They abandoned the cleartext downloads and disk-based .bat files in favor of highly obfuscated, fileless execution techniques.
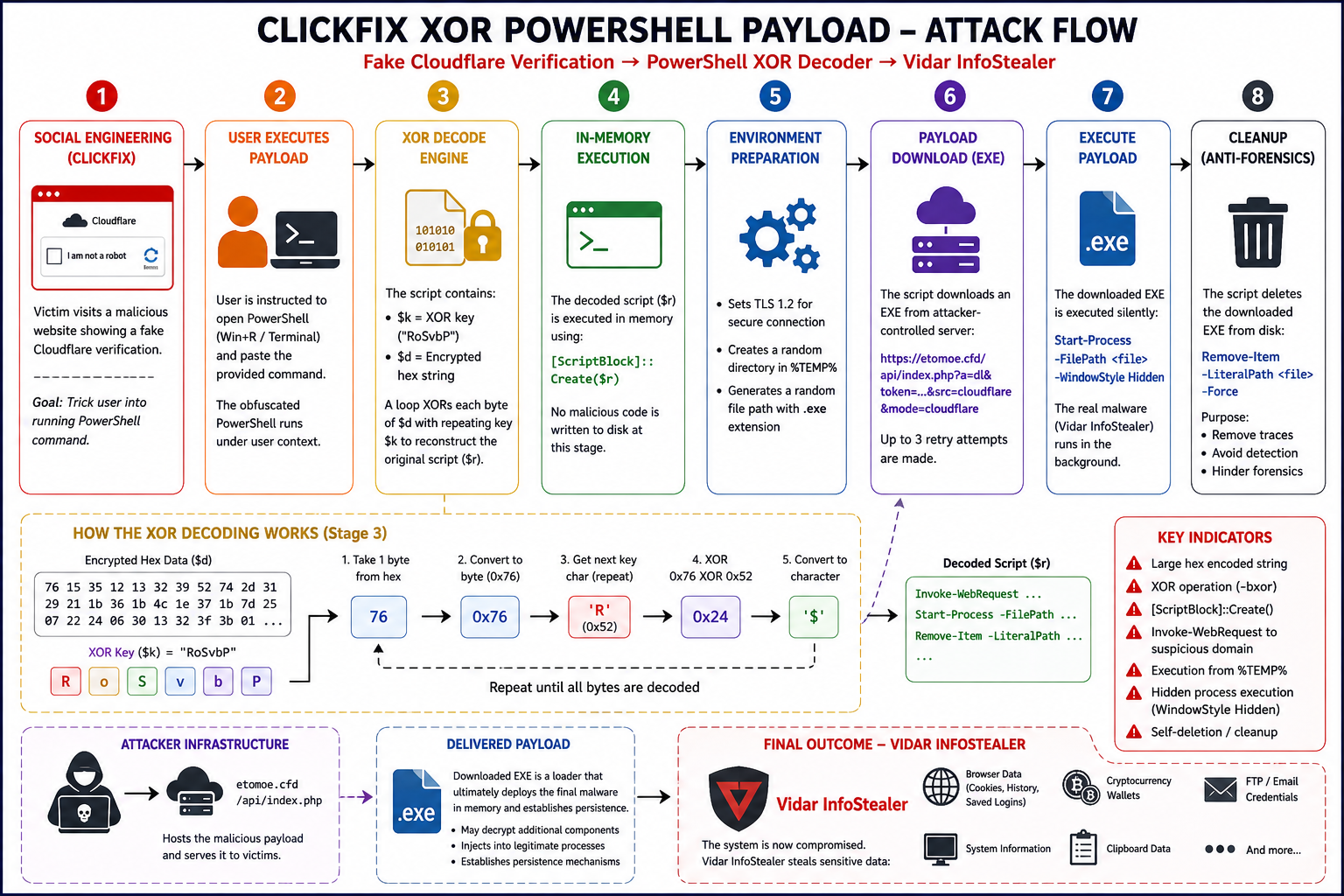
Instead of a single, predictable script, the newer variants utilize either XOR-based encryption or Base64 + Deflate compression. These scripts decode themselves entirely within the system's memory, effectively bypassing disk-scanning antivirus engines and making forensic analysis significantly more challenging. This evolution marked a shift toward a much stealthier delivery mechanism, setting the stage for a more advanced evasion technique.
The most dangerous aspect of the modern ClickFix campaign is its use of Server Side Polymorphism. While the newer variants might look like two completely different attacks one using XOR encryption and the other using Base64 encoding they are actually two sides of the exact same campaign, both ultimately designed to deliver the Vidar InfoStealer.
Server-Side Polymorphism means that the attacker's server dynamically generates a unique, newly obfuscated payload for every single victim request. When a user clicks the fake CAPTCHA, the server decides on the fly whether to serve an XOR-encrypted script or a Base64-compressed script. Because the structure, the strings, and the XOR keys (e.g., "RoSvbP") change with every download, signature-based security tools cannot rely on static file hashes to block the attack.
Regardless of which polymorphic variant the server hands the victim, the goal is stealthy, in-memory execution:
The XOR Path: The victim receives a large block of encrypted hex data. The script uses a repeating XOR key to decrypt the payload byte-by-byte. Once the original script is reconstructed, it is executed directly in memory using [ScriptBlock]::Create().
The Base64 + Deflate Path: The victim receives a massive Base64 encoded string. The script uses [Convert]::FromBase64String() to decode the binary data, decompresses it via [IO.Compression.DeflateStream], and executes it in a hidden, isolated runspace using Pipeline.Invoke().
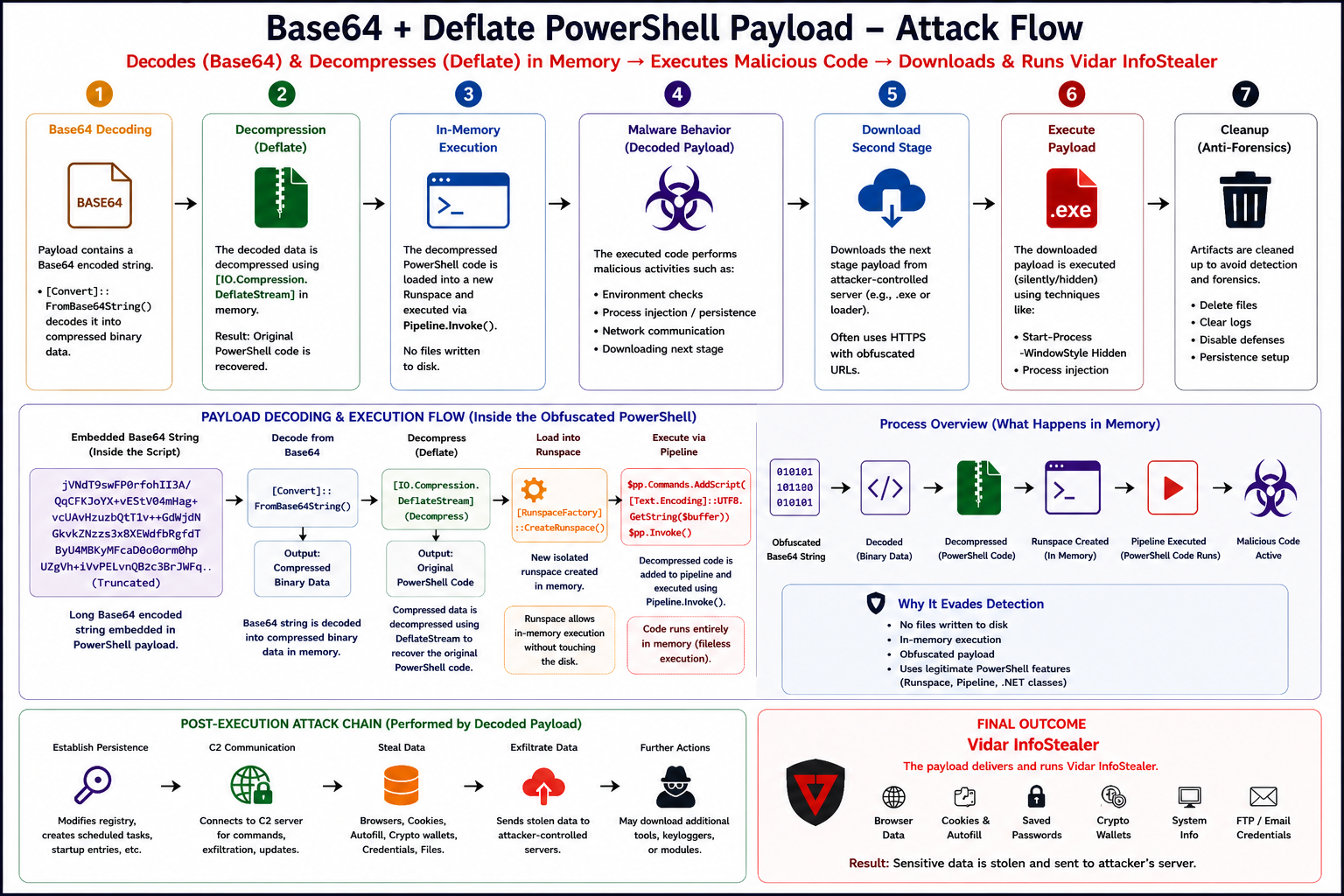
In both scenarios, no malicious code is written to disk during the decoding phase. The decoded PowerShell script silently reaches out to the attacker's infrastructure (such as etomoe.cfd), downloads an executable, runs it hidden in the background, and then deletes the original EXE to hinder forensics.
According to tracking by Menlo Labs, this polymorphic campaign has been highly active and is currently surging. Telemetry shows the campaign initiated around March 25, 2026, with a massive spike in victim targeting in late April and early May. Notably, this upward trend has not slowed down; attacks are still actively increasing throughout May. This consistent, growing volume proves that this multi-stage evasion dynamic is highly successful at slipping past traditional perimeter defenses.
Defending against fileless execution and server-side polymorphism requires security solutions that inspect code behavior before it reaches the endpoint.
Menlo Security's isolation core and dynamic analysis engines are uniquely positioned to halt this threat. Because Menlo executes web code in an isolated cloud browser, it successfully identifies the malicious intent of the ClickFix infrastructure before the victim can even copy the PowerShell command.
As observed in our telemetry, when users attempt to access the malicious infrastructure (such as the payload hosting domain chubrik[.]sbs), Menlo Security successfully intercepts the connection. The platform classifies the request as "Zero Hour Malicious" and issues a Website Blocked warning, effectively neutralizing the social engineering attempt and preventing the PowerShell payload from ever reaching the user's clipboard.
Security teams should monitor for the following network indicators and file artifacts associated with this campaign. Notably, Menlo Labs has identified over ~4.5K domains that belong specifically to this "Server-Side Polymorphism" campaign, demonstrating the massive infrastructure powering these evasive attacks. What makes this even more critical is that the majority of these domains are still currently live and operational.
Because of this sheer volume, relying solely on static domain blocklists is ineffective.
For the complete, updated list of the ~4.5K identified domains, please reference here: https://pastebin.com/raw/KCD9yCRu
Menlo Security
