The Next Billion Users Will Not Be Human: Menlo Security Launches Industry’s First Browser Security Platform
Details

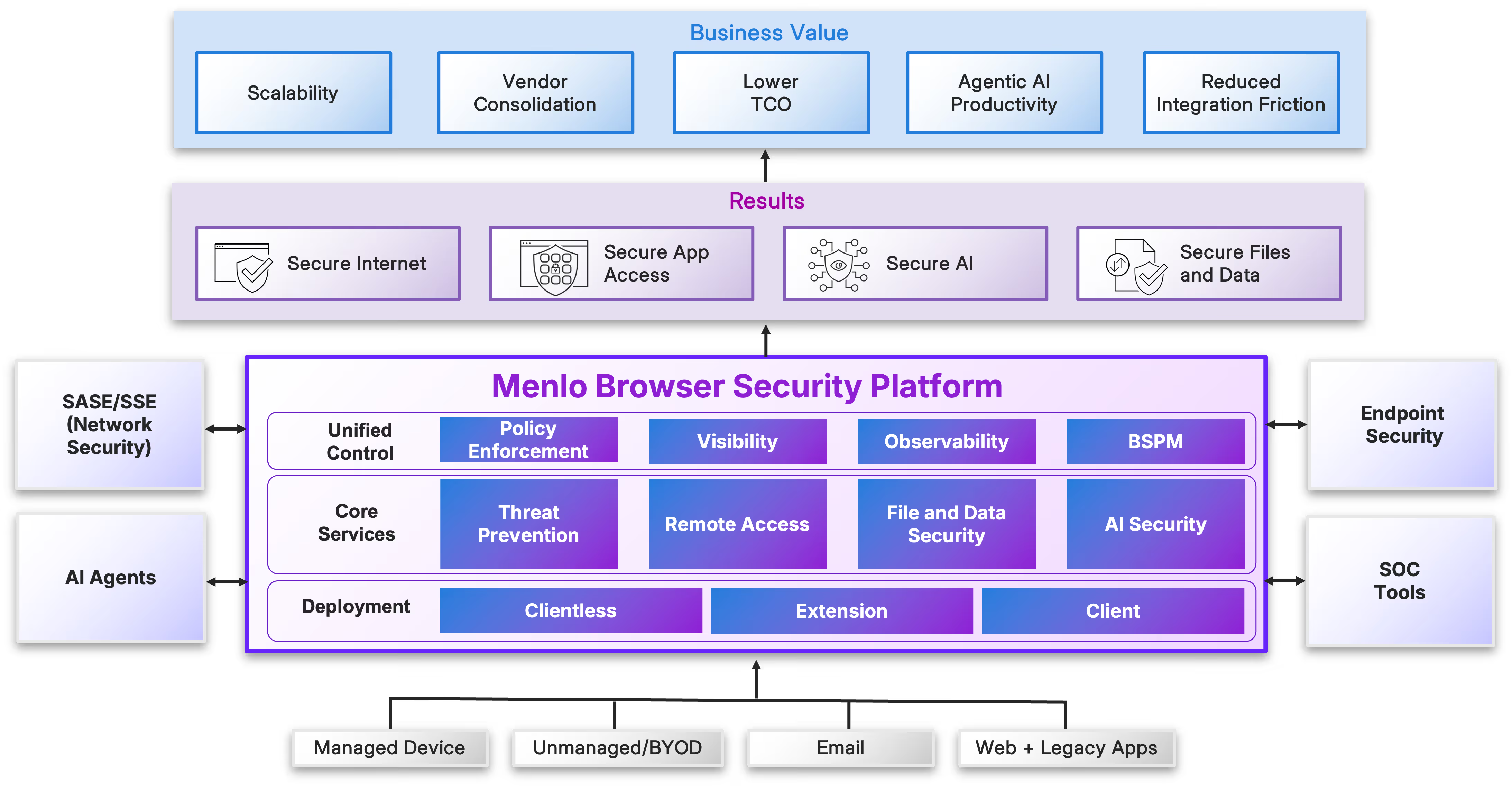
The browser is where humans and AI agents get their jobs done.
The Menlo Browser Security Platform secures and enables productivity for both.
Through a single control plane, with the elastic cloud scale required to meet the fluid needs of your agentic strategy, Menlo delivers architectural immunity for all your users, human and silicon.



























Read Report

Read Report


Read Report

Unique Hybrid Architecture: The first and only solution to combine local security controls with cloud-based protection.
Intelligent Local Controls: The Menlo Secure Extension delivers Browser DLP and visibility for user interactions with trusted sites and web applications.
High-Risk Protection: High-risk browsing activity is automatically routed to the Menlo Cloud for cloud rendering and threat elimination.

Bridging Agents to Data: ConnectAI workflows to trapped enterprise data. Menlo acts a secure bridge for applications with no or deficient APIs, connect agents and AI workflows to theapplications and data they need.
Intelligent Navigation: Navigates through complex web UIs to enable agent workflows.
Agent Access: Enables agents and AI workflows to easily navigate with SaaS and customerweb applications without complex scripts or setup.
Eliminates Modernization Debt: Solves "agentic data starvation" without requiring expensive, time-consuming system overhauls.
Immediate ROI: Enables CIOs to extract AI-driven value from existing legacy infrastructure today.

Unified Browser Security: Treats humans and AI agents as equal participants, applying tailored policies to meet the specific needs of each.
Single Control Plane: Delivers unified tools, policies, and observability for consistent security across every sessioSn
Comprehensive Protection: Ensures zero-day threat prevention, file security, and data protection are applied regardless of the actor.
Confident AI Adoption: Resolves the "Agentic Paradox," allowing the enterprise to safely unlock the productivity gains of AI agents.

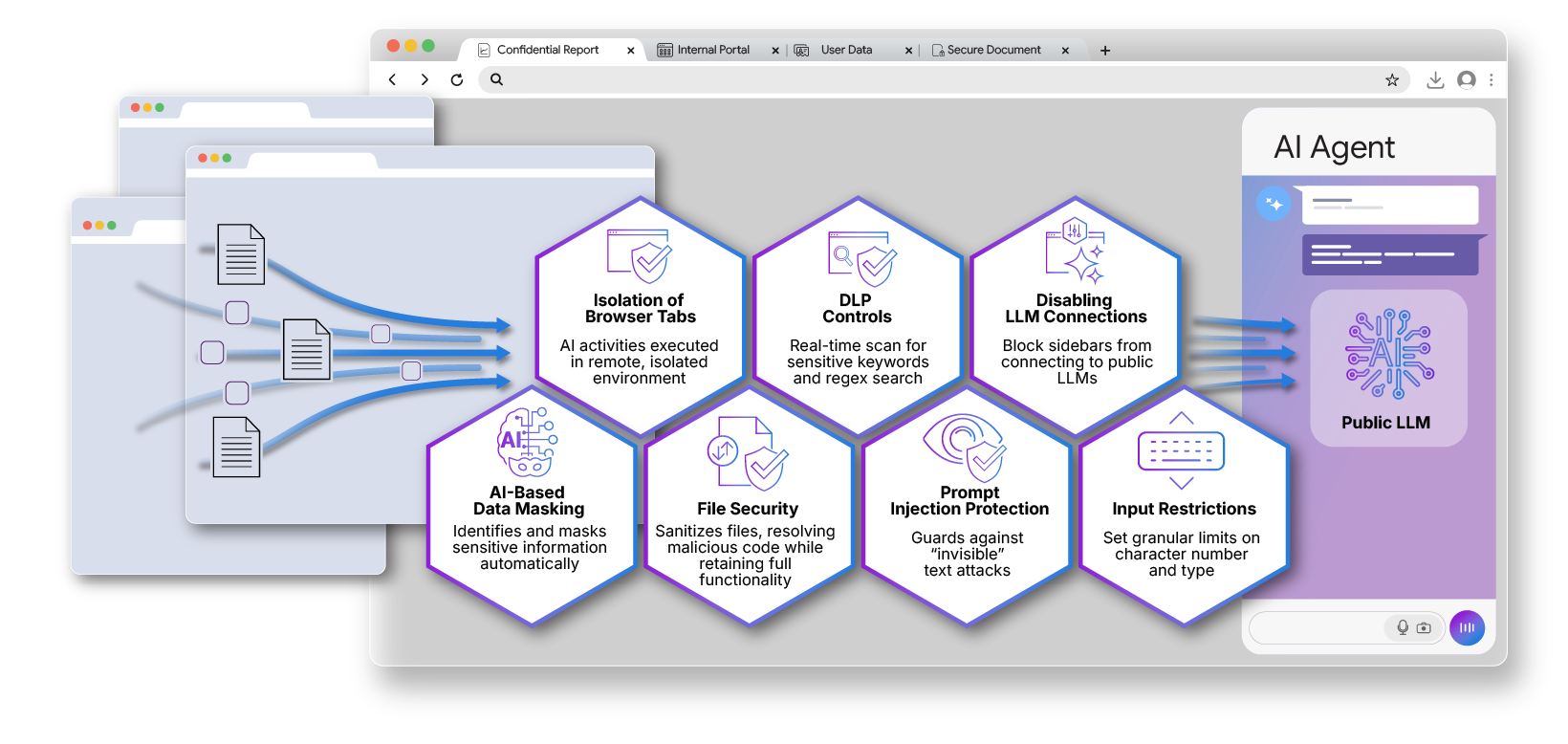
Modern browsers now include unmanaged, autonomous browser agents by default, and these create a new threat vector,
Menlo extends AI Agent Security to the browser agent, actively applying security controls and prefiltering what the sidebar can see and access. Menlo gives enterprises the controls and visibility needed to safely enable users to realize the productivity gains of browser agents without the risks of data loss and malware ingestion.
As enterprises build strategies to deploy AI agents, they face fundamental challenges that threaten to limit the productivity gains from agentic AI, while simultaneously creating new and profound security exposures.
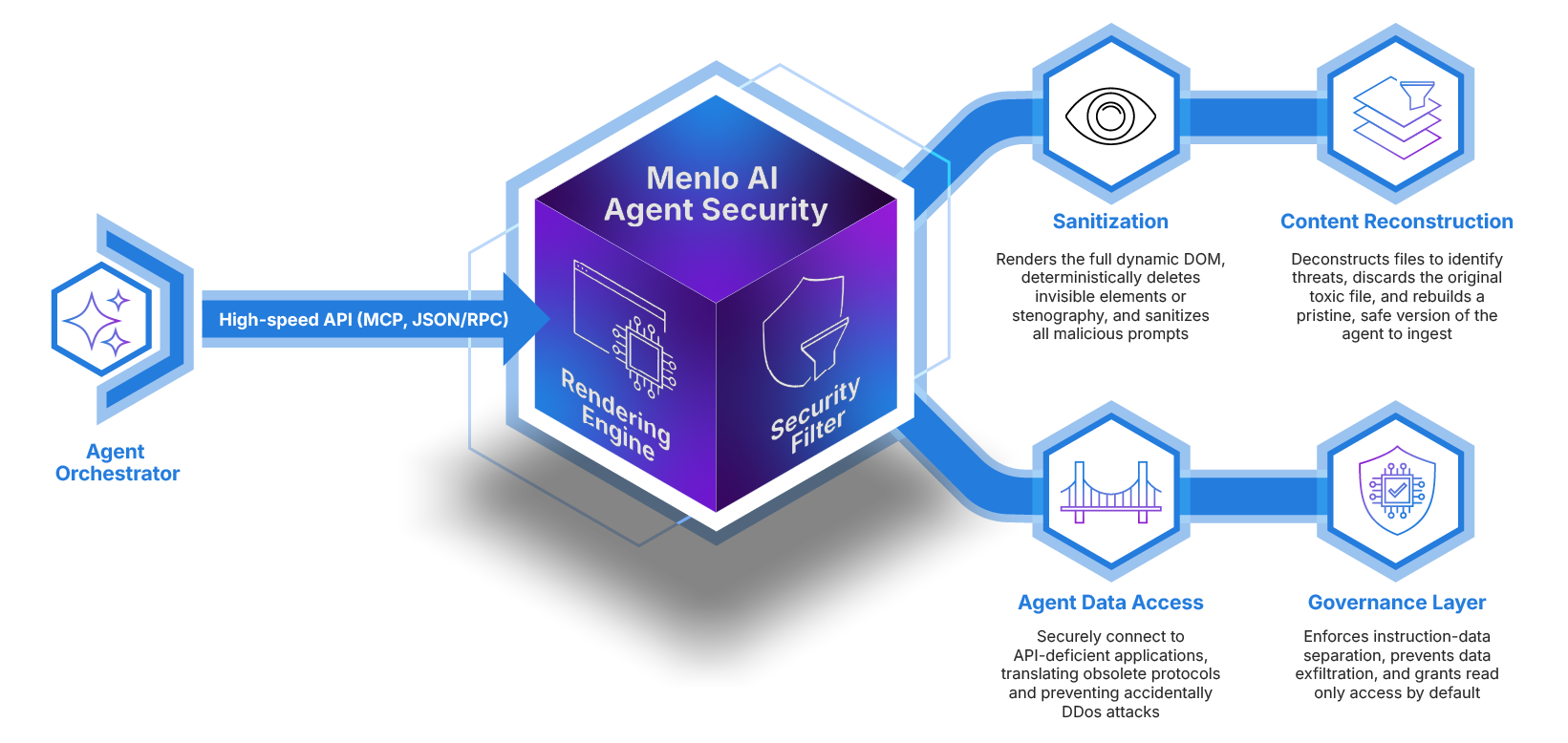
Menlo AI Agent Security, part of the Menlo Browser Security Platform, resolves the "Agentic Paradox." By providing a hardened guardian runtime, Menlo secures agent workflows and bridges the gap to trapped enterprise data. AI Agent Security delivers immediate ROI, making agents instantly productive and safe. With unified observability and zero-day prevention, Menlo provides the definitive security layer for both humans and your silicon workforce.
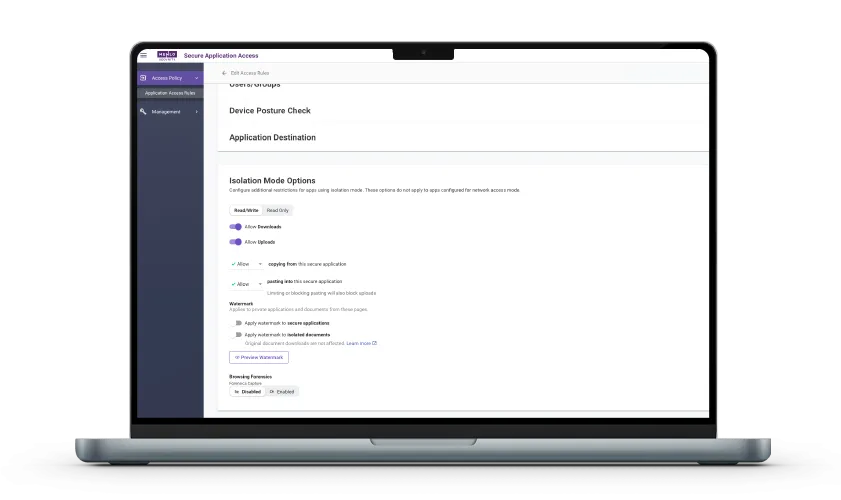
Take a self-guided tour to observe some of the ways that Menlo products enable secure app access, block sophisticated attacks, and provide critical insight into browsing sessions.
See exactly how Menlo can be tailored to solve your unique security challenges. We offer a live demo customized to your teamʼs goals, showing you how to secure your stack and protect your users. A truly secure browsing experience is one click away.



The clientless, cloud-native path to retiring your vulnerable VPN.
VPN Replacement


Deliver zero-trust through standard browsers with zero infrastructure changes, removing the high cost and complexity of legacy ZTNA.
Zero Trust Access


Eliminate the cost, complexity and performance issues of VDI with a streamlined, cloud delivered solution that secures access for all users and devices with no infrastructure overhaul.
VDI Reduction


Enable agentless secure access to SaaS and private apps for unmanaged devices while ensuring compromised endpoints never reach your apps, files, or data.
BYOD Security


Immunize your autonomous agents and the agents in your users’ browsers from goal hijacking and inadvertent or maliciously directed data exfiltration.
Protecting Agentic AI


Modernize your apps and provide time to value for agentic investments by connecting agents to API-deficient internal and external data sources quickly and easily.
Unlocking Agentic Data Access


Go beyond traditional signatures-based detection and protect against unknown phishing attacks targeting the browser with real-time, AI-powered threat prevention.
Phishing Prevention


Stop polymorphic ransomware in the cloud before it ever reaches your devices or penetrates your network perimeter.
Evasive Ransomware


Gain unprecedented visibility into browser sessions for fast incident resolution, threat hunting, audit/compliance, and more.
Browsing Visibility


Enable safe access to generative AI platforms while protecting enterprise data and intellectual property.
Generative AI Governance


Stop file-borne threats that go beyond the browser, including web downloads, portal uploads, and email attachments.
File Security


Stop unauthorized exposure and exfiltration of sensitive data and corporate IP by humans or agents, masking data in the source file while leaving the file ready for sharing or consumption
Data Protection


Use zero trust security to isolate your people and data from threats while providing fast, secure access to apps.
Government Agency Security


All that you expect from SSE with lower cost and complexity, plus browser security.
Browser SSE


Take a self-guided tour to see how Menlo blocks attacks, secures apps, and provides browsing insight.
Product Demos and Tours

