In the relentless cat-and-mouse game between threat actors and defenders, phishing infrastructure has evolved from simple credential harvesting into sophisticated operations with multi-layered defensive mechanisms. Menlo Security has identified a massive, persistent campaign active since June 2025, approximately 3.4K malicious domains.
This campaign utilizes a highly obfuscated, aggressive phishing kit assessed with high confidence to be a variant of Sneaky 2FA specifically designed to impersonate Microsoft 365 login portals. Its primary objective is not just to steal passwords, but to harvest session cookies, allowing attackers to bypass Two-Factor Authentication (2FA) and authenticate directly to corporate services.
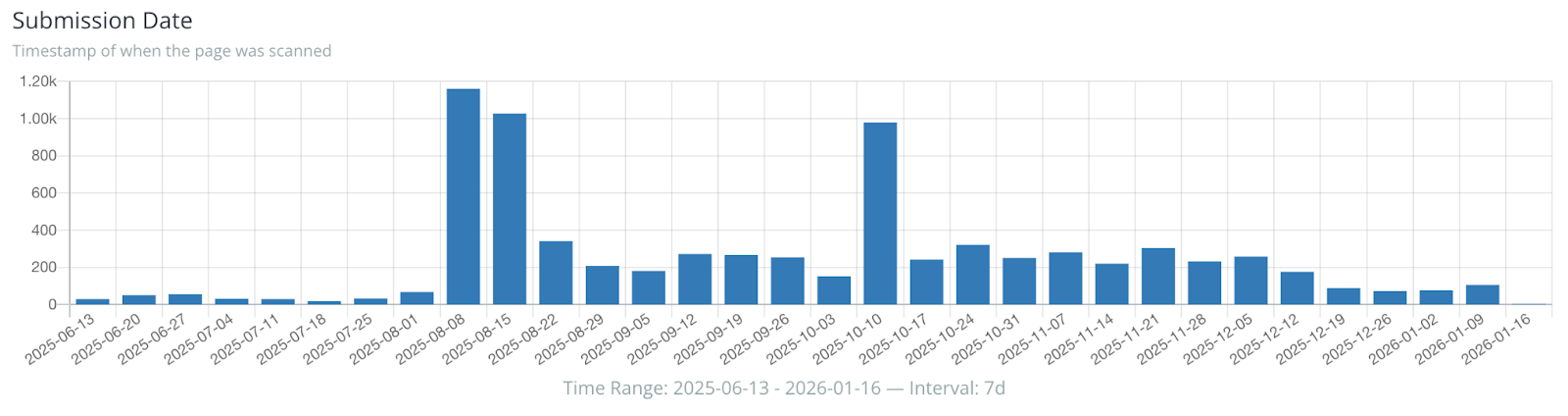
Figure 1: Timeline of campaign activity showing persistence from June 2025 to Jan 2026
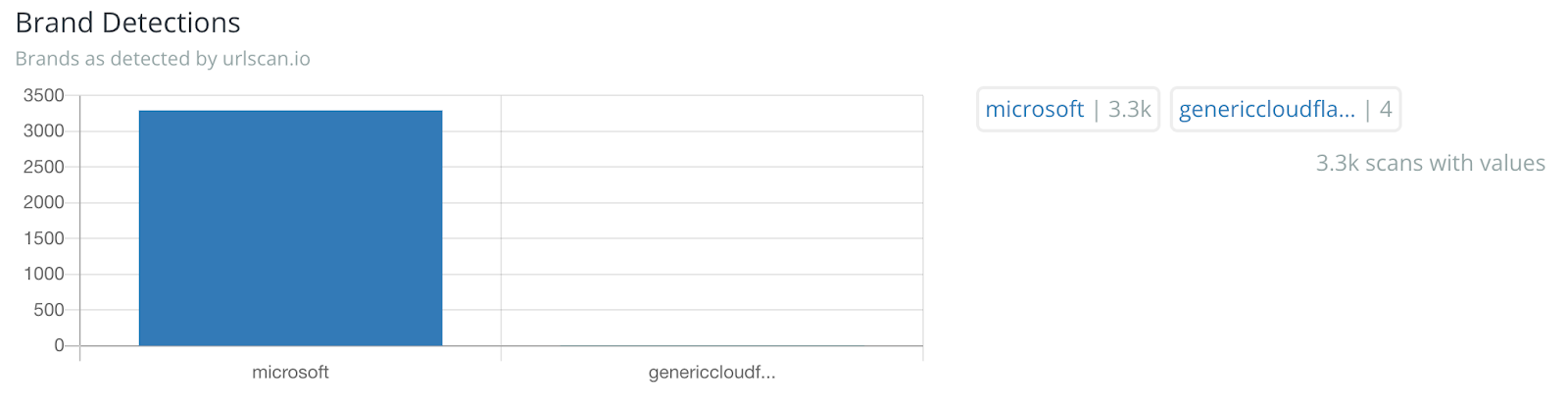
Figure 2: Graph showing the volume of the ~3.4K associated domains
The attack begins with a highly deceptive delivery mechanism designed to bypass email gateways and static file scanners.
During our investigation on VirusTotal, we identified a PDF containing embedded malicious URLs. The PDF is engineered to leverage social engineering, using reassuring language like “Your security is our priority” to appear genuine. The visual design, featuring a prominent PDF icon and repeated ‘Review Document’ prompts, creates a sense of urgency, pushing the user into a "click-whirr" psychological response.
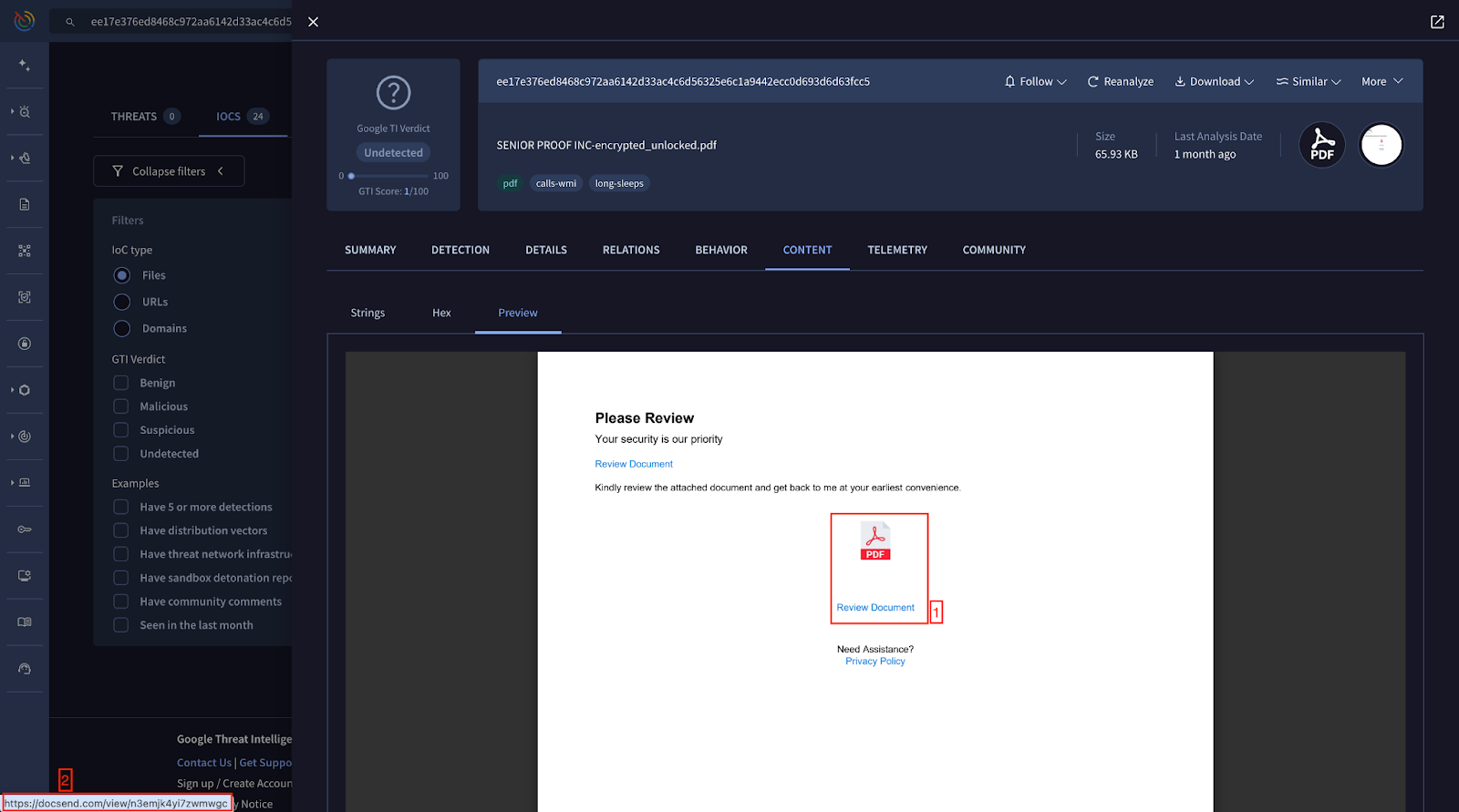
Figure 3: Attack Correlation - Screenshot of the PDF Lure with "Review Document" button
Zero-Day Detection Evasion: Crucially, VirusTotal did not flag this PDF as phishing or malicious. It passed through all vendor checks without a single warning (0/60 detection rate). This demonstrates that the attackers carefully crafted the file structure to stay under the radar of signature-based detection systems.
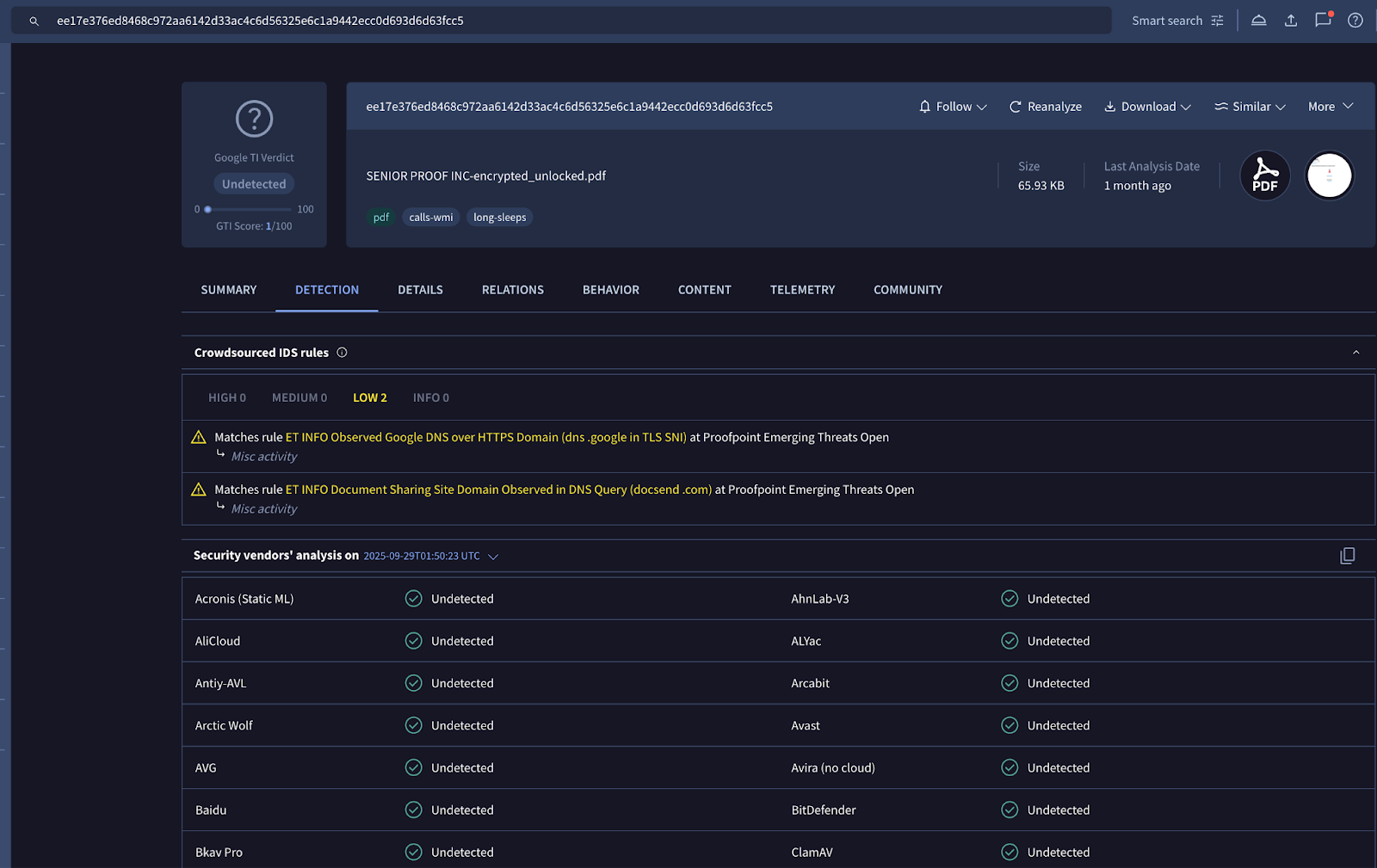
Figure 4: VirusTotal detection screenshot showing 0 detections
The Phishing Flow: Once the user clicks the link in this lure, they are redirected to a malicious website (the "Initial Gate") instead of opening a real document. This site initiates the technical attack chain described below.
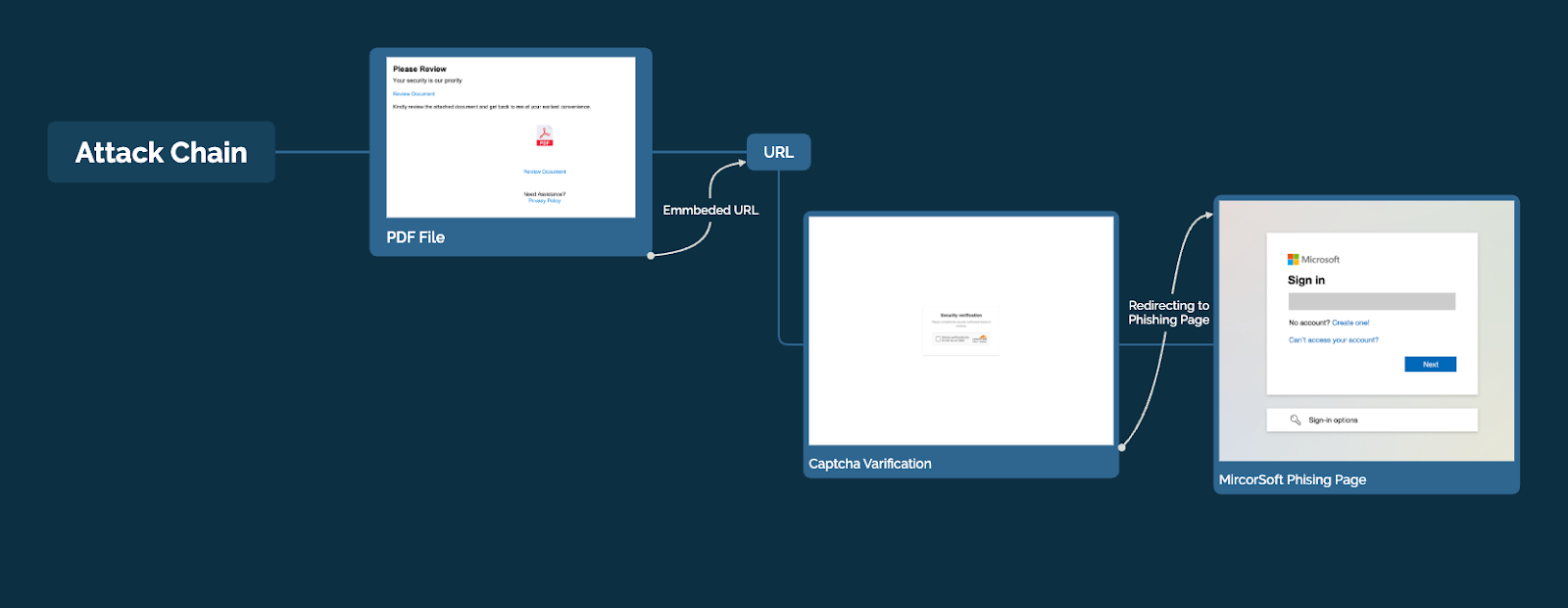
Figure 5: Phishing Flow Diagram - PDF -> Redirect -> Turnstile -> Landing Page
The attack chain functions as a filter, admitting only genuine human interactions while aggressively shedding automated scanners.
The victim is initially directed to a page titled "Please wait...". While visually benign, this page serves as a psychological anchor for the user and a staging ground for client-side scrutiny.
Figure 6: Please wait Tiled Page
The kit integrates Cloudflare Turnstile immediately. Unlike traditional CAPTCHAs, Turnstile uses passive telemetry to verify human origin. This is the first layer of filtration against simple web crawlers and URL scanners.
Figure 7: Screenshot of “the Security Verification”
HTML Evidence: Turnstile Integration
<script src="https://challenges.cloudflare.com/turnstile/v0/api.js" async="" defer=""></script>
...
<div class="x_csul5f03ndmzbxpft5p3">
<div class="cf-turnstile" data-sitekey="0x4AAAAAACJnArganjmhqSf8" data-theme="auto" data-size="normal" data-callback="secFunc_Elakuguvud_Ihawetog_dbc71718">
<div><input type="hidden" name="cf-turnstile-response" id="cf-chl-widget-xfz5w_response"></div>
</div>
</div>
The data-callback attribute executes “secFunc_Elakuguvud..”. only after a successful token is generated. This ensures that the core malicious payload remains dormant if a scanner cannot pass the Turnstile check.
The DOM contains hidden input fields meant to trap automated form-fillers.
Bots often indiscriminately fill all input fields in the DOM. A human user cannot see these fields (due to left: -9999px). If data is received in these parameters, the server immediately flags the client as automated and terminates the session.
HTML Evidence: Hidden Fields
<div style="position: absolute; left: -9999px; top: -9999px; visibility: hidden;">
<input type="text" name="website" id="website" tabindex="-1" autocomplete="off">
<input type="email" name="confirm_email" id="confirm_email" tabindex="-1" autocomplete="off">
<input type="text" name="phone_verify" id="phone_verify" tabindex="-1" autocomplete="off">
</div>
Upon passing the Turnstile check, the kit aggregates granular behavioral data to validate the victim quality.
JS Evidence: Analytics Payload Construction
var analyticsData_ab395cee = {
userEngagement: userActivity_a3daf980, // Mouse movements/interactions
inputMetrics: inputEvents_2fc36fb7, // Keyboard events
sessionTime: Date.now() - sessionStart_fb8317e3, // Dwell time
qualityScore: qualityMetrics_b8bea522 // Boolean pass/fail of env checks
};
appendInput_e9143878(form_df822f73, 'analytics_data', JSON.stringify(analyticsData_ab395cee));
The qualityScore variable captures client-side behavioral signals and is sent to the backend together with the Turnstile token. This type of data is often used by modern phishing kits to separate real users from automated scanners or sandbox environments, and to adjust their evasive action based on page interaction.
The core sophistication of this kit lies in its JavaScript, which employs a "checkmate" strategy against researchers.
The page text is fragmented to defeat keyword-based static analysis.
HTML Evidence: Text Fragmentation
<span class="show_Apurip">S</span>
<span class="hide_Giruke" style="display:none;">Z</span>
<span class="show_Danefu">e</span>
<span class="hide_Osolez" style="display:none;">E</span>
<span class="show_Iwegaj">c</span>
...
A string search for "Security Verification" will fail. The browser renders the text visually, but the raw HTML contains garbage characters (Z, E, O hidden via CSS) that corrupt the text stream for parsers.
The kit aggressively defends against analysis tools.
1. Timing Attacks:
The script inserts a debugger statement and measures execution time. If a researcher's DevTools are open, the browser pauses at the breakpoint. The script detects this pause (execution time > 205ms) and redirects the user.
JS Evidence: Debugger Timing Check
const debugTimeS_Pirato_Rojo_0e906616 = performance.now();
debugger; // Intentional breakpoint
const debugTimeE_Nokane_Hobu_093fb2a2 = performance.now();
if (debugTimeE_Nokane_Hobu_093fb2a2 - debugTimeS_Pirato_Rojo_0e906616 > 205) {
window.location.href = 'about:blank#debugger-pause';
}
2. Console & Shortcut Blocking:
The kit suppresses runtime visibility by overriding console.log and related console methods, effectively silencing debug output. It also deploys a console-detection technique that leverages JavaScript getters on Image objects, a method commonly used to infer whether browser developer tools are open or actively inspecting objects.
JS Evidence: Console & Shortcut Blocking
const devKeys_Wociba_Gipa_34f14b45 = e.keyCode === 123 ||
(e.ctrlKey && e.shiftKey && e.keyCode === 73); // Block F12, Ctrl+Shift+I
if (devKeys_Wociba_Gipa_34f14b45) {
window.location.href = 'about:blank#shortcut-blocked';
return false;
}
The kit queries low-level hardware properties to detect virtualized environments used by security vendors.
JS Evidence: Hardware Concurrency & Memory
// Detect weak hardware (common in sandboxes)
if (navigator.hardwareConcurrency <= 2) { /* Flag as suspicious */ }
if (navigator.deviceMemory && navigator.deviceMemory <= 2) { /* Flag as suspicious */ }
// Detect Headless Browsers & Automation
if (window.navigator.webdriver) { /* Flag as bot */ }
const suspiciousAgents_25155397 = ['HeadlessChrome', 'PhantomJS', 'Selenium'];
JS Evidence: Graphics & Canvas Fingerprinting
const webglContext_e16aa3e7 = canvasElement.getContext('webgl');
const renderer_13e36fdc = webglContext_e16aa3e7.getParameter(webglContext.RENDERER);
Detect virtualized GPUs
const suspiciousRenderers_84b7f159 =
['SwiftShader', 'ANGLE', 'Microsoft Basic Render Driver','VMware', 'VirtualBox', 'Chromium', 'Mesa DRI','llvmpipe', 'Software Rasterizer', 'Google Inc.','NVIDIA Corporation (Virtual)', 'AMD (Virtual)','Intel Inc. (Virtual)', 'Parallels', 'QEMU'];
Real user devices rarely use software renderers like "SwiftShader" or have only 2GB of RAM. These signatures specifically target the default configurations of malware analysis sandboxes.
Based on the code structure, the specific use of href.li redirects, and the rigorous anti-analysis logic, we assess with high confidence that this campaign utilizes a variant of the Sneaky 2FA phishing kit.
Sneaky 2FA Characteristics Observed:
If the victim passes all checks, they are redirected via href.li (to strip the referrer) to a legitimate site (techterms.com) before hitting the final spoofed Microsoft 365 login.
JS Evidence: Redirect Configuration
const phpConfig = {"random":"https:\/\/href.li\/?https:\/\/techterms.com\/definition\/microsoft#google_vignette"};

Figure 8: The Redirect Chain: Phishing Page -> href.li -> techterms -> Microsoft Spoof
This campaign demonstrates that modern phishing is no longer a simple lure directing the user to a static webpage, but a combination of a lure with a site featuring dynamic, multi-layered defenses. . The use of Turnstile, heavy obfuscation, and real-time environment checks renders legacy, reputation-based blocking ineffective.
Menlo Security detects this threat by analyzing the rendered DOM within the browser isolation core.
Figure 9: Menlo HeatShield Alert Dashboard showing the blocked threat
Menlo Security
