
Since mid-January 2019, Menlo Security has witnessed an uptick in the Emotet Trojan activity across our customer base, Based on our research we wanted to share some of the interesting observations.
Emotet dates back to 2014 and has been evolving ever since then. Emotet was originally designed as a banking malware that attempted to steal sensitive and private information from infected endpoints. As the campaign evolved, the Emotet group added the ability to be a malware delivery service—including to other banking Trojans. According to a US-CERT alert published in 2018, “Emotet continues to be among the most costly and destructive malware affecting state, local, tribal, and territorial (SLTT) governments, and the private and public sectors.” Based on the Emotet activity we saw across our logs, we will focus this blog on three of its aspects:
We have seen the Emotet malicious document delivered in two different ways:
The following chart shows a distribution of industries being targeted by Emotet based on the data we collected in January 2019.

Based on the same data, the click-time category distribution for the websites hosting the malicious documents is shown below. (Each click to a link is categorized using the standard categorization databases available.)

The Business category is the most prominent; hosting malicious files behind legitimate categories makes this attack increasingly difficult to detect.
We have also seen these malicious documents delivered via email attachments. The following is a sample of the email “Subject:” header values and “From:” address domains used.

It is not surprising that these infected documents are using embedded macros to deliver the Trojan, as this is very typical of Emotet. In the set of documents, we saw, 80 percent were disguised as Word documents with a .doc extension, but they were actually XML files. This technique is probably used to evade sandboxes, since sandboxes typically use the true file type and not the extension to identify the application, they need to run in inside the sandbox. While the true file type is XML, it is still opened in Microsoft Word at the endpoint, thereby prompting the user to enable the malicious embedded macro. The remaining 20 percent of malicious documents we saw were standard Word documents with an embedded malicious macro. For 10 percent of the malicious files we saw, the antivirus (AV) scan results were unknown (in other words, none of the AV vendors classified the initial document as malicious).
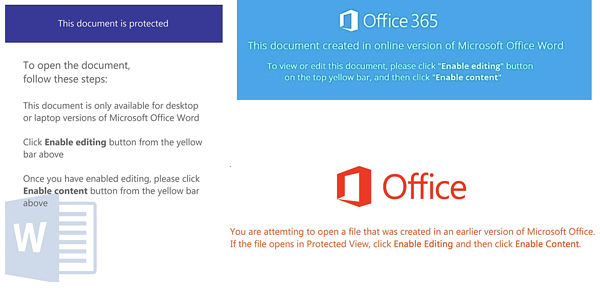
The content of the initial documents used different message themes with the appropriate Microsoft Office logos to trick the user into enabling the embedded macro in the document.
In some documents, we observed that viewing the contents of the macro was disabled, and the VBA Project was locked down, possibly with an intent to thwart the analysis of the macro’s contents.

We saw two different types of malicious document formats used.
The first type, and the more prominent one, was an XML file that contains the standard XML header, plus the Microsoft Word Document XML format tags. This is followed by Base64 encoded data, which contains the compressed and obfuscated VBA macro code. The file itself was named with a .doc extension.

The technique of disguising a Word document as an XML document with Base64 encoded data is probably done to evade antivirus detection. Looking at our log data for these files, the click-time antivirus scan results for these files had a poor detection ratio.

The second type of documents consisted of regular Microsoft Word documents that had a malicious embedded macro in them.
The embedded VBA macro was highly obfuscated, with dead code insertion. The macro ends up calling a shell function with the vbHide parameter set. Some interesting points on how the remaining commands get built after the shell function gets called from the VBA macro:

Example VBA making call to “Shell” function, with the “vbHide” parameter set:

Example CMD/PowerShell script from one of the observed samples making use of “Invoke-DOSfucation” techniques.

After successful execution of the PowerShell script, we saw that the final delivered payload was the Emotet Trojan, which establishes a command-and-control channel with the attacker’s infrastructure. Over the years, Emotet has become highly customizable, so the attackers can use this command-and-control channel to send additional malware.
www[.]ploeger[.]ru
id14[.]good-gid[.]ru
zobzarrinco[.]ir
aziendaagricolamazzola[.]it
dmoving[.]co[.]il
expoluxo[.]com
kamdhenu[.]technoexam[.]com
ldztmdy[.]cf
mstudija[.]lt
puntodeencuentrove[.]com
somov-igor[.]ru
www[.]purifiq[.]co[.]za
www[.]topstick[.]co[.]kr
hxxp://stoutarc[.]com/JbCOGyE
hxxp://www.modern-autoparts[.]com/ezFUGpI
hxxp://antigua.aguilarnoticias[.]com/LNOGFuYx
hxxp://uicphipsi[.]com/4d20qS_izTLi7wu1_uuk
hxxp://vuonnhatrong[.]com/FSrJps_iKqwbRFjH
hxxp://themissfitlife[.]com/5wn_YAsyS0M
hxxp://evoqueart[.]com/Wk0MdRvGzW
hxxp://leptokurtosis[.]com/wmK5XminG
hxxp://mimiabner[.]com/tvprRKdT
7c5cdc5b738f5d7b40140f2cc0a73db61845b45cbc2a297bee2d950657cab658
37a000cd97233076cd3150c4dbde11d3d31237906b55866b7503fdc38cd1de08
Untitled_attachment_22012019.doc
2050822044828453.doc
ATT2469528456278769653.doc
PAY199472702716599.doc
altopro[.]com[.]mx
bir[.]gov[.]ph
cafemarino[.]com[.]mx
daawat[.]com[.]pk
ecop[.]org[.]ph
iata[.]org
insular[.]com[.]ph
insurance[.]gov[.]ph
lbstation[.]co[.]uk
phil-union[.]com
rubiconeng[.]com
telkomsa[.]net
thielenhaus[.]cn
trmdemexico[.]com
wbf[.]ph
application/xml and filename endswith .doc
NOTE: Most of the above-mentioned URLs/domains might no longer be active.
In the past, we have seen Emotet being delivered through regular macro-infested Word documents, but this technique of disguising an XML document as a Word document seems to be a recent change in the delivery technique. With such constant changes in tactics from the Emotet threat actors, we foresee that this campaign will continue to evolve and become more sophisticated. In 2018, we observed that Emotet was among the top banking Trojans, and we expect this trend to continue in 2019.
Check out the Remote browser adoption overview from Gartner and Magic Quadrant for Secure Web Gateway to see why Menlo Zero Trust solutions continue to be the answer to security concerns.
----------------------------------
References
Menlo Security
