The Next Billion Users Will Not Be Human: Menlo Security Launches Industry’s First Browser Security Platform
Details




Agentic AI has shifted the enterprise operating model, establishing the browser as the new enterprise OS. As organizations scale AI agents that navigate, authenticate, and execute tasks at machine speed, they expose a critical gap: traditional security is built for humans, not autonomous agents.
Replacement browsers and extensions are architecturally incapable of securing this new workforce, as agents often operate via headless browsers or serverless containers outside the local device. Legacy stacks are equally blind; SASE secures the "pipe" and EDR protects the host OS, but neither provides the session-level visibility needed to defend against the unique vulnerabilities of the agentic enterprise.













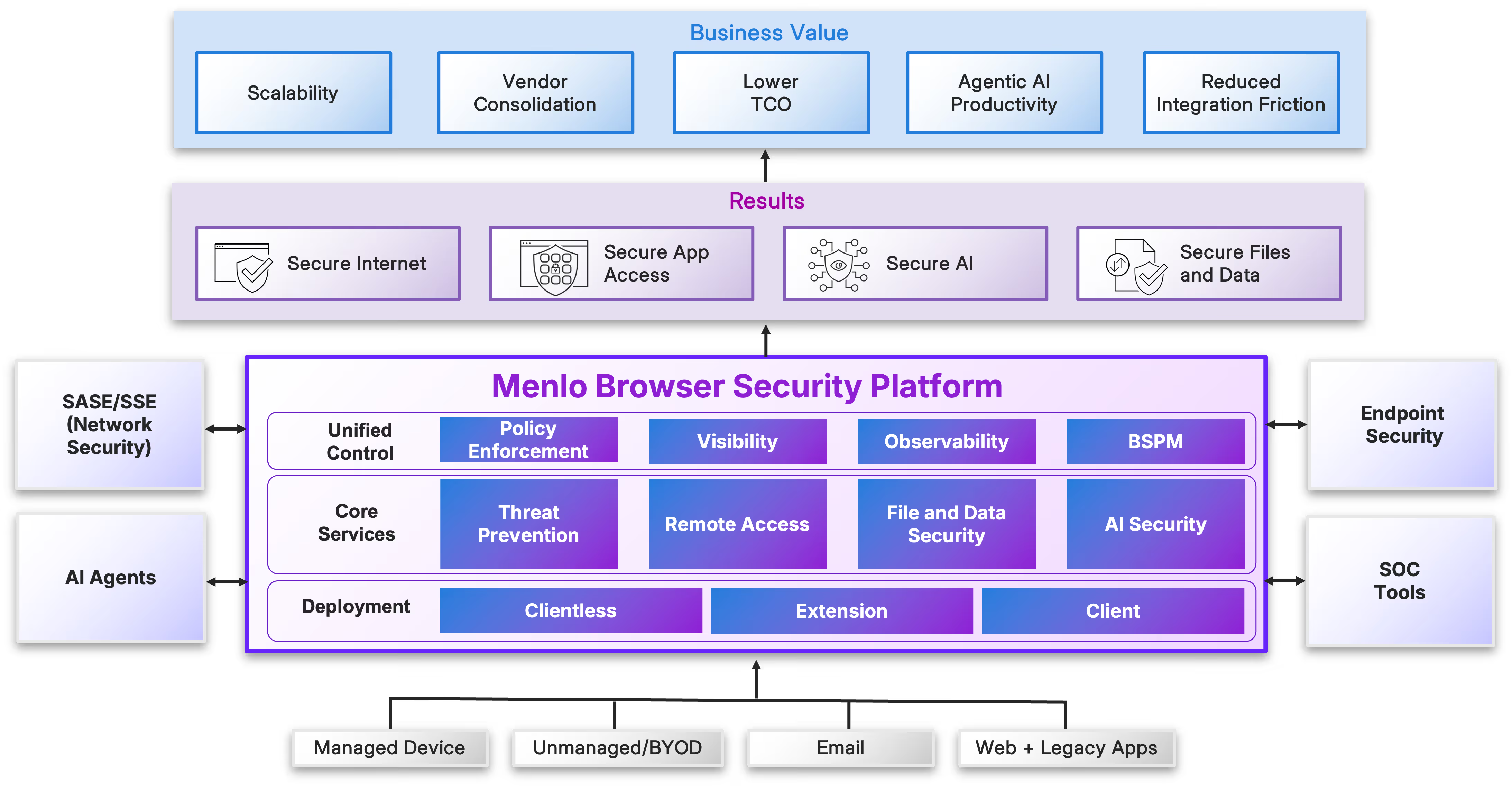
The Menlo Browser Security Platform collapses the distance between security, productivity, and innovation, eliminating the compromise between security and the speed of modern business. It is a cohesive defense system that deploys a suite of core capabilities at cloud scale to provide architectural immunity for both humans and AI agents. A single control plane delivers unified tools, policies, and observability and ensures that zero day threat prevention, file and data security, and secure access to applications are applied consistently across every session, regardless of the actor, channel or device.
Adaptive Defense: Dynamically adjusts security levels based on real-time session risk.
Optimized SaaS: Provides native performance, visibility, and data control for trusted apps.
Invisible Isolation: Offers total air-gapped protection for high-risk browsing and agentic AI interactions.
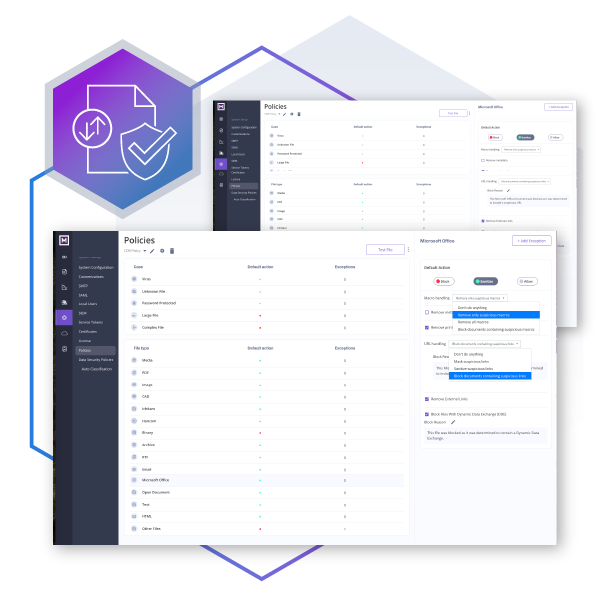
Unified Control: Manages the entire environment through a single, streamlined policy plane.
Identity Parity: Treats human employees and AI agents as equal participants in the workforce.
Unified Security Stack: Provides a single browser-based defense for all interactions, regardless of the actor.
Universal Policy Enforcement: Applies the same security rigor to human browsing and autonomous serverless agents via one central policy.
Consistent Governance: Eliminates the need for separate rules for AI, ensuring "same-rigor" protection across the board.
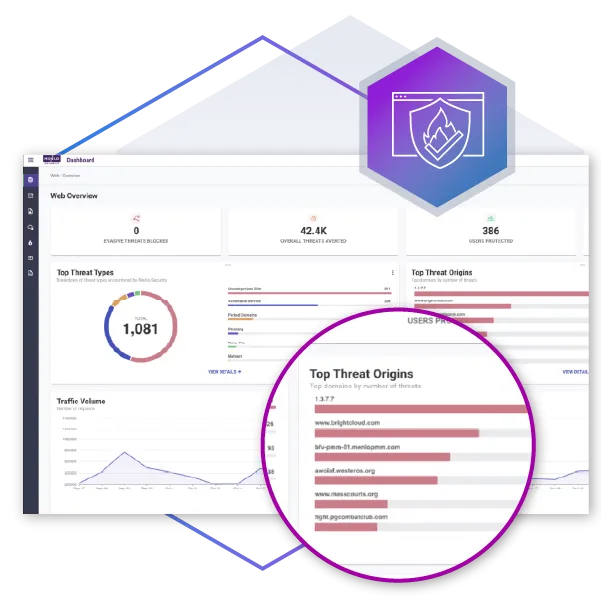
Superior Forensic Intel: Offers unified observability that outperforms fragmented data from stitched-together logs.
Unified Session Flow: Provides a single, comprehensive view of the entire session for total context.
Holistic Monitoring: Simultaneously validates data protection, threat analysis, and GenAI guardrail performance.
Policy Verification: Ensures application access policies are functioning correctly and as intended.
Eliminates Workflow Friction: Replaces restrictive "No-based" security with automated tools that reduce helpdesk tickets and manual workarounds.
Intelligent File Sanitization: Menlo File Security strips malicious code and macros while preserving the document’s original format, templates, and functionality.
Real-Time Data Masking: Menlo AI Adaptive DLP redacts sensitive information within documents without blocking access to the files themselves.
Seamless Safety: Enables humans and AI agents to collaborate freely by delivering sanitized, safe-to-use versions of documents instantly.
Beyond Signatures: Bypasses the limitations of traditional detect-and-respond tools that struggle with signature-less zero-day attacks.
Architectural Immunity: Neutralizes evasive threats in the cloud before they ever reach the user or AI agent.
Proactive AI Defense: Uses computer vision and dynamic content analysis to identify and strip away malicious code in real-time.
Execution Prevention: Shifts from "reacting" to an attack to maintaining an environment where threats are fundamentally unable to execute.
The Menlo Browser Security Platform protects both human users and AI agents, seeing inside the browser session itself to neutralize threats in the Menlo Cloud before they ever reach the user’s endpoint or are “seen” by the agent. Menlo secures every human and agent session in a cloud-isolated environment with deep, deterministic defense to instantly detect and eliminate zero-day exploits and highly evasive threats, including:
These protections are more vital than ever, as attackers are increasingly adopting the adversarial use of AI to come up with new or dramatically adapted threats, and are increasingly targeting autonomous AI agents.
Pre-Render Neutralization: Blocks zero-day phishing, brand impersonation, and polymorphic attacks before the page even renders in the browser.
Outpaces Signatures: Identifies and stops evasive social engineering long before traditional signature-based tools can flag them.
Transparent Security: Operates invisibly in the background, allowing users to work with confidence without disruptive security hurdles.
AI-Optimized Runtime: Provides a dedicated, secure environment specifically designed to protect autonomous agents.
Deterministic Defense: Identifies and neutralizes "invisible" attacks embedded in web pages or files before they can execute
Blocks Hidden Commands: Stops malicious instructions that humans can't see but agents mistakenly process as valid prompts.
Advanced Remediation: Focuses on detecting and fixing threats within the data stream to ensure agents remain safe and functional.

Menlo Secure Application Access (SAA) is a zero trust, cloud-delivered solution providing effortless and safe access for modern workforces- including employees, contractors and other unmanaged endpoints- and AI agents. Menlo Secure Application Access (SAA) is a zero trust, cloud-delivered solution providing effortless and safe access for your hybrid workforce.
Menlo SAA moves beyond simple network access to enforce highly detailed Least-Privileged Access for humans and agents connecting to SaaS, private, and legacy applications. Applications and their data are protected with DLP controls and file security, enabling safe zero-trust use of SaaS, email, collaboration tools, and cloud storage, with unparalleled control over sensitive information. SAA delivers frictionless access that maintains native user experience for both web-based and legacy applications, giving the enterprise a way to effectively replace costly, cumbersome VDI infrastructures and onboard contractors in minutes instead of days.
Zero Trust Foundation: Delivers identity-based access by treating every device as untrusted until fully validated.
Secure BYOD: Safely enables access from unmanaged or high-risk personal devices while keeping corporate data protected.
VDI Replacement: Reduces infrastructure costs and complexity by providing a modern alternative to traditional VDI deployments.
Universal Connectivity: Supports all users and endpoints across both modern web-based and legacy thick-client applications.
Least-Privileged Access: Limits AI agents to the specific data and applications required for their assigned tasks, preventing unauthorized data extraction.
Lateral Movement Prevention: Blocks compromised agents from "hopping" between tasks or infiltrating internal systems.
Comprehensive Data & File Security: Applies real-time DLP and file sanitization to stop agents from consuming sensitive data or spreading malicious content.
Air-Gapped Isolation: Segregates compromised agents from application servers to protect the core infrastructure.
Current file security tools force a critical trade-off: block workspace productivity to prevent threats from malware and other malicious content in files, or trust that detection alone will stop malware from entering in the first place. This is unacceptable for modern, file-reliant workflows.
Menlo File Security delivers defense-in-depth by incorporating next-gen Content Disarm and Reconstruction (CDR). Menlo File Security uses patented Positive Selection® technology, assuming that all files are malicious and immediately deconstructing files to their constituent elements, removing unsafe elements like embedded malware and malicious macros, and reconstructing a new, clean file using only components guaranteed to be safe. Pristine files are delivered within the user’s workflow in near real-time. This process eliminates evasive malware, ransomware, and zero-day file exploits (even those hidden in archives or password-protected files) while ensuring the final document retains its formatting and functionality.
Preserves Full Functionality: Delivers safe, fully functional files in their original formats, avoiding the usability issues of "flattened" PDFs.
Precision Sanitization: Removes only malicious content while keeping templates, macros, and active elements intact for the user.
Eliminates Productivity Roadblocks: Prevents the "blanket stripping" of data that typically leads to broken workflows and excessive help desk tickets.
Seamless User Experience: Empowers the workforce to stay productive by providing clean, usable documents without traditional security trade-offs.
Mitigates AI Vulnerabilities: Counters AI agents' lack of skepticism and removes hidden commands that humans can’t see.
Prevents Goal Hijacking: Blocks invisible "prompt injections" that could lead to compromised agents or lateral movement.
Pre-Exposure Sanitization: Cleanses every document before an agent processes it, ensuring safe data consumption.
Ensures Task Integrity: Keeps automated agents focused on their intended goals while protecting the broader enterprise from automated threats.
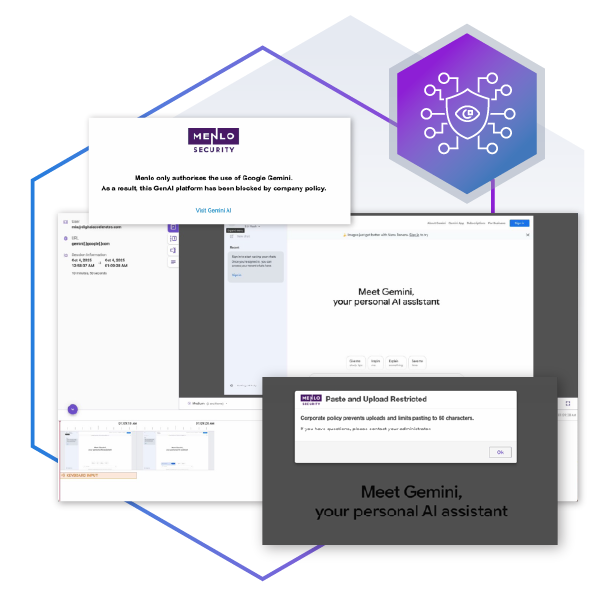
Traditional security tools fall behind the needs of the modern, hybrid workforce. DLP tools block file usage, impeding collaborative workflows for humans and data gathering for AI agents. DSPM tools are reactive, generating alerts after detecting irregularities but not performing any remediation.
Menlo AI Adaptive DLP delivers automatic, real-time, AI-based detection and masking of the most common sensitive data types, including PII, PHI, and financial data fields such as those subject to PCI standards, and includes extensible detection to protect unique corporate IP. It masks only sensitive data in the file, leaving the file otherwise pristine and available for consumption and sharing.
Menlo AI Adaptive DLP eliminates the friction between compliance and productivity caused by DLP false positive detection errors, keeping humans and agents working without requiring manual intervention or the disabling of automated enforcement. It deploys quickly and easily, eliminating the need for cumbersome RegEx-based configuration and endpoint agents with AI-powered detection rules and a cloud delivery model with zero-footprint on the endpoint.
Pervasive Data Protection: Protects across email, SaaS apps, web portals, storage, and all browser-based uploads/downloads.
Dynamic Data Masking: Automatically applies redaction only when and where it is needed to keep enterprise data safe.
Workflow-Centric Security: Operates transparently in the background, ensuring security never disrupts the user’s natural way of working.
Secure Collaboration: Empowers users to share and interact freely while maintaining strict guardrails against data leakage.
Prevents Automated Data Harvesting: Blocks agents from blindly scraping PII, credentials, or trade secrets in pursuit of their tasks.
Pre-Access Masking: Intercepts data streams to redact sensitive corporate IP before the agent can process it.
Maintains Task Focus: Ensures agents only consume safe, relevant data, preventing accidental or malicious data exfiltration.
Zero-Friction Productivity: Allows agents full use of non-sensitive content within pages or files so they remain functional and on-task.