
If you think the little green lock of https equals security, think again. The bad news is that the bad guys use encryption too. Many people mistakenly assume that as long as an SSL certificate is present, they’re safe from attack, but that couldn’t be further from the truth. From Reductor to Godlua and numerous other variants, it has become all too clear that new types of malware are being secreted behind a symbol that was once seen as secure.
Enterprises have long relied on on-premises proxies (and next-generation firewalls) for visibility and control of web access. But when it comes to decrypting and inspecting SSL sessions, many enterprises have held back partly driven out of privacy issues and partly around performance of these proxies with SSL decryption turned on. It’s not uncommon for the overall throughput of these devices to drop by a factor of five (or more) when SSL decryption is turned on. That means for the same number of employees surfing the web, they would need five times more devices to keep up the same throughput. This choice didn’t affect the top line of security (much) when back in 2015, only 6.71% of the top 1 million Alexa websites were available over https.
Fast forward to 2019, this is now 51.78%! This rapid rise in https adoption has largely been driven by a few factors. Starting in 2014, Google started including https as a ranking signal for search results. That meant websites served over https had a higher likelihood of showing up in search results than those without. Recent versions of Chrome and Firefox have started to aggressively warn the user about a website not being secure if it’s not served over https (especially if it contains forms). Finally, thanks to Certificate Authorities like Let’s Encrypt, it became trivial for websites, web developers and even bad actors to easily enable https, have it auto renewed. What used to be a chore was simply automated away. For enterprises that have chosen not to inspect SSL, the 51% statistic means that their security blindsightedness (not accounting for mobile, etc.) has conservatively grown 8 times in 4 years!
In Menlo’s own Global Cloud Platform where we proxy and isolate billions of web sessions for our enterprise customers, some of these statistics strongly support the case for SSL Inspection. We are going to look at three different views of web sessions: Web navigation, Clicks on email links and Non-Browser (machine-generated) sessions. All of the data below is based on the last 30-days of activity on our platform.
These are web sessions initiated by the user by navigating to websites – by directly typing the URL in the browser – via search results or via bookmarks. Compared to the 51.78% statistic in the top 1M websites, our Global Cloud Platform is seeing 96.7% of all user initiated web visits being served over https! This is significant for enterprises, because without SSL inspection, these users are not being protected on the web at all.

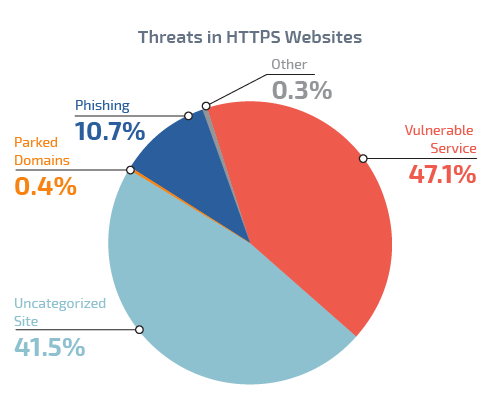
Breaking down the threats in https websites, we find that 47.1% of the https websites are running vulnerable server software (like an old version of Apache, Drupal, Wordpress, etc.)
The Menlo Global Cloud Platform includes an email link/attachment rewriter that allows our users to safely open email links in isolation. We first look at the protocol of the URLs in email links irrespective of if the user clicked on them. 57.7% of the URL links in emails turns out to be https, meaning that the on-premises web proxy or next-gen firewall will be oblivious to the threats on these websites unless the enterprise chooses to turn on SSL inspection and take the performance hit.

The real risk though is when a user clicks on the link. 92.1% of the websites that the user clicked to visit were over https, including known and unknown phishing sites!

Non-Browser web sessions, as seen by our Cloud Platform, is typically generated by endpoint agents downloading various updates, but also includes C2 (Command & Control) callbacks from infected endpoints. We find that 66.8% of the non-browser traffic is over SSL.

Breaking the https sessions down by the known threat (as classified by our platform), we note that 90.6% of the machine-generated https sessions are to uncategorized websites. In addition 0.005% of these sessions were to known malware or phishing sites.

The stats from our Global Cloud Platform clearly show that the Internet (good and bad) is largely on its way to moving to https. Enterprises that don’t perform SSL inspection because of the lack of performance on their on-premises proxy are at a much higher risk now than even just a few years ago. So how can enterprises embrace SSL inspection and reap the security rewards?
One of the key benefits of a cloud proxy is the ability to elastically scale SSL inspection without any performance degradation. Unlike hardware appliances that are spec’d out for peak loads, the cloud allows us to automatically scale to meet the demand, never incurring the performance penalty nor degrading security. Enterprises no longer need to make these trade-offs and they can truly get security without the compromise – the answer lies in the cloud.
Menlo Security
