The Next Billion Users Will Not Be Human: Menlo Security Launches Industry’s First Browser Security Platform
Details


Everyone loves the cloud for the same reasons: elastic scale, centralization, agility, collaboration, and access to advanced technology sooner. So why does cloud-based remote browser isolation (RBI) have a bad reputation?
There has to be a better way to get cloud-based browser security, and there is: Menlo Cloud-Based Browser Security.
For any browser, and for every user, in every location, Menlo creates a secure digital twin browser in the cloud. What happens next is the advanced technology that enables cloud-based browser security to work for the modern web. Menlo Advanced Cloud-Based Browser Security is enabled by patented Adaptive Clientless Rendering.
Both pixel streaming RBI and Menlo leverage a twin browser in the cloud. But Menlo is more carefully maintained: both major and monitor updates are applied within 72 hours or faster if critical. While the secure digital twin browser requires updates, other components of the cloud architecture are static and immutable for risk reduction. Pixel-streaming checkbox RBI does not receive the same attention and care.

Every endpoint is over-burdened with security applications, libraries and dangerously, kernel-resident components. Advanced cloud-based browser security doesn’t add to this burden. Operating without a requirement to install anything, Menlo Advanced Cloud-Based Browser Security operates by sending minimal, secure active code to the browser that enables modern cloud based browser security.

Menlo Advanced Cloud-Based Browser Security operates by understanding and optimizing for security on every page’s Document Object Mode (DOM), which is a dynamic, browser-internal representation of how the web page should be rendered. The browser combines the DOM with Cascading Style Sheets (CSS) to render page content.
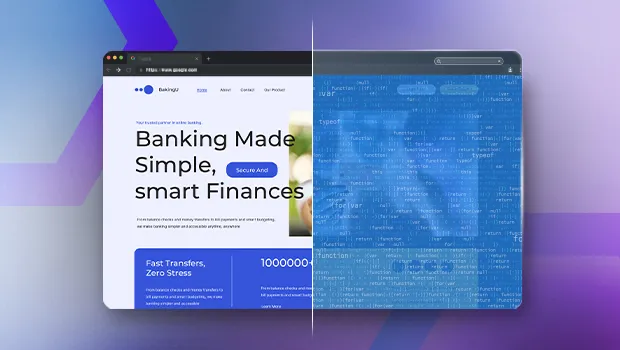
Cloud-based rendering enables advanced detection of fraudulent web sites.

Advanced Cloud-Based Browser Security replaces the architecture of pixel-stream, first-generation RBI, which renders pages in the cloud, delivering web content as images. First-generation RBI wastes the powerful rendering resources available in every endpoint today – both desktop and mobile. Menlo ACR delivers only safe HTML to the endpoint for rendering.

Advanced Cloud-Based Browser Security assumes all active code is harmful and prevents it from reaching the endpoint. To enable broad compatibility with modern web usage, active content is executed only in the cloud to help ensure, for example, accurate rendering.

Advanced Cloud-Based Browser Security assumes images may contain malware. Images are rendered in the cloud, verified as safe and then transmitted. Risk reduction for audio and video content is accomplished by upstream verifications including URL risk scoring.

Replacing legacy RBI with Advanced Cloud-Based Browser Security has worked for thousands of organizations worldwide. You do not have to accept insecure, endpoint-based browser security. You can enjoy all the benefits that cloud delivers applied to browser security.
Preemptive browser security requires cloud interception of threats. But it has to be done right, and that’s what the Menlo Cloud delivers: Advanced Browser Security that leverages endpoint rendering for efficiency and scale.
Synapxe, the Singapore national healthtech agency, tried legacy RBI. Apps broke and slow browsing compromised productivity. Then, when Synapxe adopted Advanced Cloud-Based Browser Security, help desk calls complaining about browsing performance stopped.
The enterprise security team always faces conflicting mandates: security and a combination of user satisfaction and efficiency. Advanced cloud-based browser security helps security teams fulfill them all. Unlike replacement browsers, advanced cloud-based browser security works with any web application, on endpoint browser, for every type of user, anywhere they work. Read about typical pixel-stream limitations. Read about performance and compatibility problems with replacement browsers.

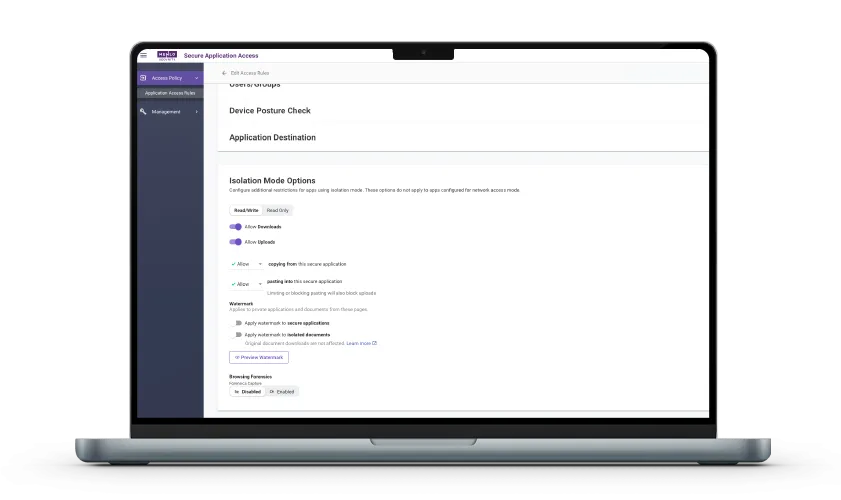
From a use-case perspective, the Menlo Cloud is used for both Menlo Threat Prevention and Menlo Secure Application Access. The solution elements described above are used directly in our offerings:
The Menlo Cloud prevent threats to users, their organizations and internal web applications by removing active code from web content, delivering only safe web content to web browsers. Efficient endpoint rendering enables use cases like VDI reduction, even across the WAN.
Secure Access to internal applications is routed from users' browsers through the Menlo Cloud, sending only safe HTML to internal applications.
Another security team mandate is the requirement to cover differing user communities. Some communities create challenges for other forms of browser security that require endpoint installation: BYOD, contractors, and team members coming aboard through mergers and acquisitions.
While most legacy, pixel stream RBI is architecturally agentless, the vendors that provide that aging technology almost always have a client, if for nothing else than ZTNA. A core architectural feature of the Menlo Cloud is that it does not require endpoint software installation. No Agents. No clients. No libraries. No kernel elements. No endpoint software to maintain. Traffic routing to the Menlo Cloud is non-disruptive, using mechanisms you already use and know. Menlo ZTNA is agentless as well.

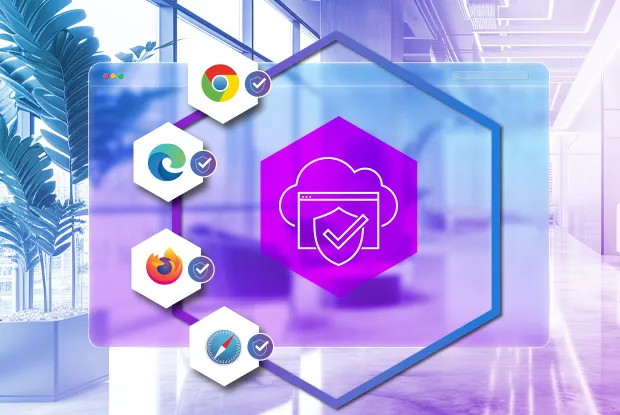
The desktop team knows that user preferences are real. iPhone and Android? Yes. PC and Mac? Sure. But what about Safari, Firefox, and Microsoft Edge?
Replacement browsers force users into a specific browser, overriding their preferences and compromising productivity.
Advanced Cloud-Based Browser Security supports any browser. Sure, legacy RBI supports any browser but it fails to scale and breaks applications. Every browser is supported with advanced browser security that also works for all web applications, even the most modern, that legacy RBI sometimes cannot render properly.
Many organizations have one too many regulations with which to comply, a problem that is massively exacerbated for global organizations. Your organization potentially requires compliance review for security solutions. What happens when the compliance team sees that the source code for browser security is visible on the endpoint, for all the world to see? This is occasionally seen with both replacement browsers and extensions offering browser security.
Advanced Cloud-Based Browser Security operates with secure code in a highly secure environment. Only lightweight Javascript enables endpoint rendering with security. Your compliance team can trust and verify that Menlo Security is much less likely to be breached than endpoint browser security solutions.

Discover why organizations around the world rely on Menlo Security to protect the enterprise and enable secure access to applications, preventing attacks that legacy security tools cannot stop.
Answers to the burning questions in your mind.


Menlo is not a replacement browser for the endpoint. There is no upside to replacing the endpoint browser as discussed in our blog series part 1 and part 2.
Rather, to accomplish cloud-based browser security, Menlo instantiates a hardened digital twin of the user's local browser. This twin fetches and executes and examines all browser traffic on behalf of the user's local browser. Then:
- Browser page content is delivered using patented Adaptive Clientless Rendering with many benefits, including high performance leveraging endpoint rendering and broad web application compatibility. Legacy RBI pixel streaming provides none of those benefits. Replacement browsers disable crucial endpoint rendering technology, which compromises performance and breaks web application function.
- Web traffic Archives are unpacked and their embedded files, as well as the files themselves, are all inspected and sanitized before delivering to the user's browser.
Instead of buying a browser, you are buying preemptive browser security!

Menlo isolates all browsers. The solution is browser-agnostic, meaning it works with and secures any local browser the user selects, including mainstream browsers like Chrome and Edge, as well as new AI-powered browsers and specialized extensions. The Menlo Cloud runs a digital twin of the local browser in the cloud, isolating all web content execution away from the endpoint, regardless of the user's browser choice.

Unlike legacy, pixel-streaming RBI offerings, Menlo Security leverages patented technology called Adaptive Clientless Rendering (ACR). ACR leverages Document Object Model (DOM) mirroring to transmit clean, lightweight web content to the endpoint to leverage the power of endpoint rendering. This approach preserves browser choice and enables secure, compatible browsing for the most complex web applications.

The primary benefit of cloud-based browser security is preemptive security that eliminates the local browser attack surface by loading and executing all web content in the cloud, ensuring that threats and malware embedded in active page content and in files never reach the user's device. Other benefits of cloud-based isolation leveraging advanced technology like ACR, rather than pixel streaming, include very high performance and low latency delivering content and files.

There are no drawbacks to remote browser isolation if it provides high security, high performance, and low latency, and, in particular, if security is transparent to end users. Menlo Advanced RBI has these characteristics.
Legacy RBI that depends on outdated pixel-streaming that was originally invented for purposes other than web browsing has many drawbacks including poor compatibility, poor performance, and painful limitations.

Unlike some legacy pixel-streaming RBI offerings stranded in a private cloud architecture, Menlo leverages leading public cloud providers. Menlo Cloud services are provided by 15 data centers worldwide equipped with ultra-fast internet connections to ensure low latency.
Take a self-guided tour to observe some of the ways that Menlo products enable secure app access, block sophisticated attacks, and provide critical insight into browsing sessions.
See exactly how Menlo can be tailored to solve your unique security challenges. We offer a live demo customized to your teamʼs goals, showing you how to secure your stack and protect your users. A truly secure browsing experience is one click away.